GNS3 — Network software emulator
The network topology was set up and configured using the Graphical Network Simulator 3 (GNS3) application. Using GNS3, networking devices can be emulated to create complex networks. Many corporations such as Walmart, AT&T, and NASA use GNS3 for testing network configurations before applying them in the real world. It is open-source and available at gns3.com.
Appliances
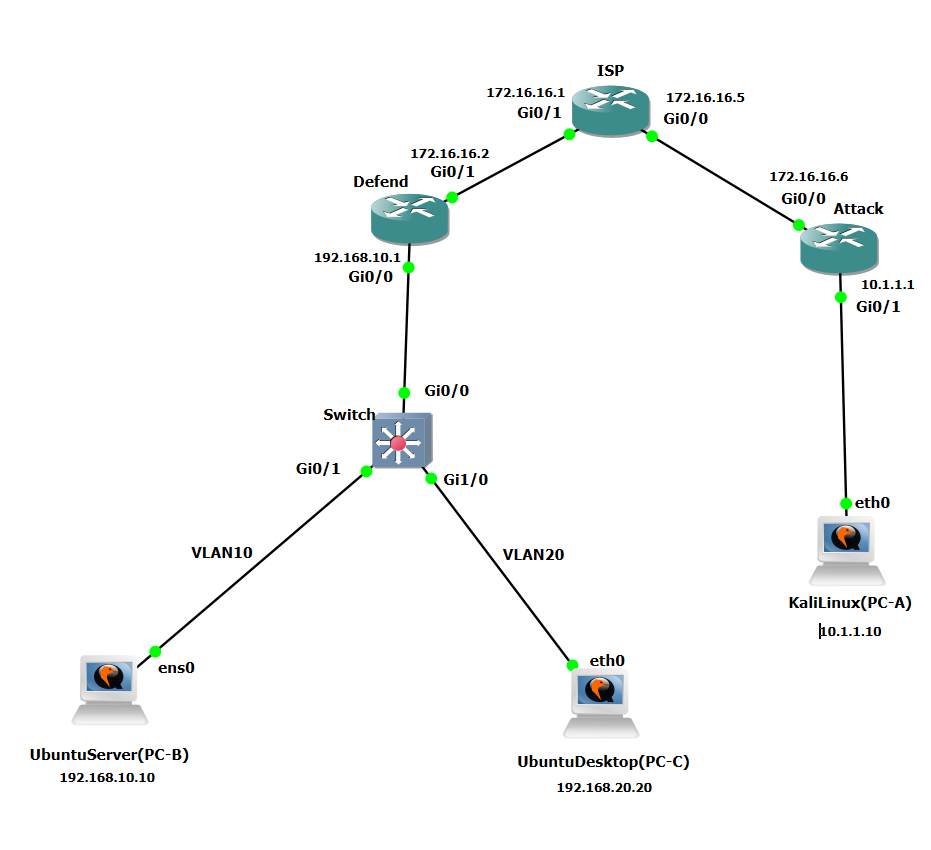
Each device in GNS3 is known as an appliance — representing the virtual devices running in the topology:
- 3x Cisco IOSv 15.7(3) routers
- 1x Cisco IOSvL2 15.2.1 switch
- 1x Kali Linux 2021.1 PC (PC – A) — Attacker
- 1x Ubuntu 20.10 PC (PC – B) — Target Desktop
- 1x Ubuntu Server 18.04.3 (PC – C) — Target Server
IP address scheme
| Device | IP / Interface 1 | IP / Interface 2 | IP / Interface 3 |
|---|---|---|---|
| Attacker's Network | G0/0: 172.16.16.6/30 | G0/1: 10.1.1.1/24 | N/A |
| ISP Router | G0/0: 172.16.16.5/30 | G0/1: 172.16.16.1/30 | N/A |
| Target Network | G0/0.10: 192.168.10.1/24 | G0/0.20: 192.168.20.1/24 | G0/1: 172.16.16.2/30 |
| Switch | G0/1: VLAN 10 | G1/0: VLAN 20 | N/A |
| VLAN 10 | 192.168.10.0/24 | N/A | N/A |
| VLAN 20 | 192.168.20.0/24 | N/A | N/A |
| Kali Linux (PC – A) | 10.1.1.10/24 | N/A | N/A |
| Ubuntu Desktop (PC – B) | 192.168.20.20/24 | N/A | N/A |
| Ubuntu Server (PC – C) | 192.168.10.10/24 | N/A | N/A |
Device configuration
Cisco Routers
Interfaces were configured per the IP addressing scheme. Unused ports were shut down. Banners were applied to enforce unauthorized access policies. An admin user was created with passwords encrypted using the scrypt hashing algorithm. A domain name of SnrProj.com was set and SSH access configured. OSPF was implemented as the routing protocol using area ID 0 with authentication enabled.
Cisco Switch
VLANs were configured per the IP scheme. All unused ports were shut down and switchport port-security was implemented on each active interface — limited to 1 MAC address, set to shut down immediately on a policy violation.
Ubuntu Server (PC – C)
Updated via temporary internet access, then statically assigned and connected to G0/1 on the switch in VLAN 10. Apache2 was installed to host web services. A domain name was configured to simulate a real-world environment. VSFTPD version 2.3.4 was specifically installed as the Metasploit exploit target.
Ubuntu Desktop (PC – B)
Updated and statically assigned per the IP scheme, connected to G1/0 on the switch in VLAN 20. An FTP user was created and VSFTPD version 3.0.3 was installed. The host file was modified to resolve the Ubuntu server's domain name.
Kali Linux (PC – A)
Statically assigned per the IP scheme and connected directly to the attack router on G0/1. All penetration testing tools came pre-installed. The host file was modified to resolve the Ubuntu server's domain name.
Network topology