Denial-of-Service attack
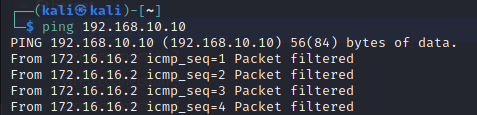
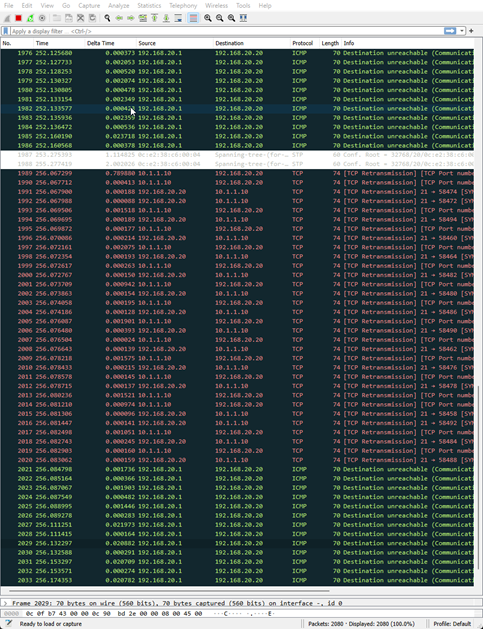
Implementing firewall rules to block malicious packets is the most effective solution. A common SYN flood pattern is that the Max Segment Size (MSS) is set abnormally high or not set at all, which can be used to filter attacks.
Configuring firewall rules
Configuring system security settings
The sysctl.conf file was edited using sudo nano /etc/sysctl.conf:
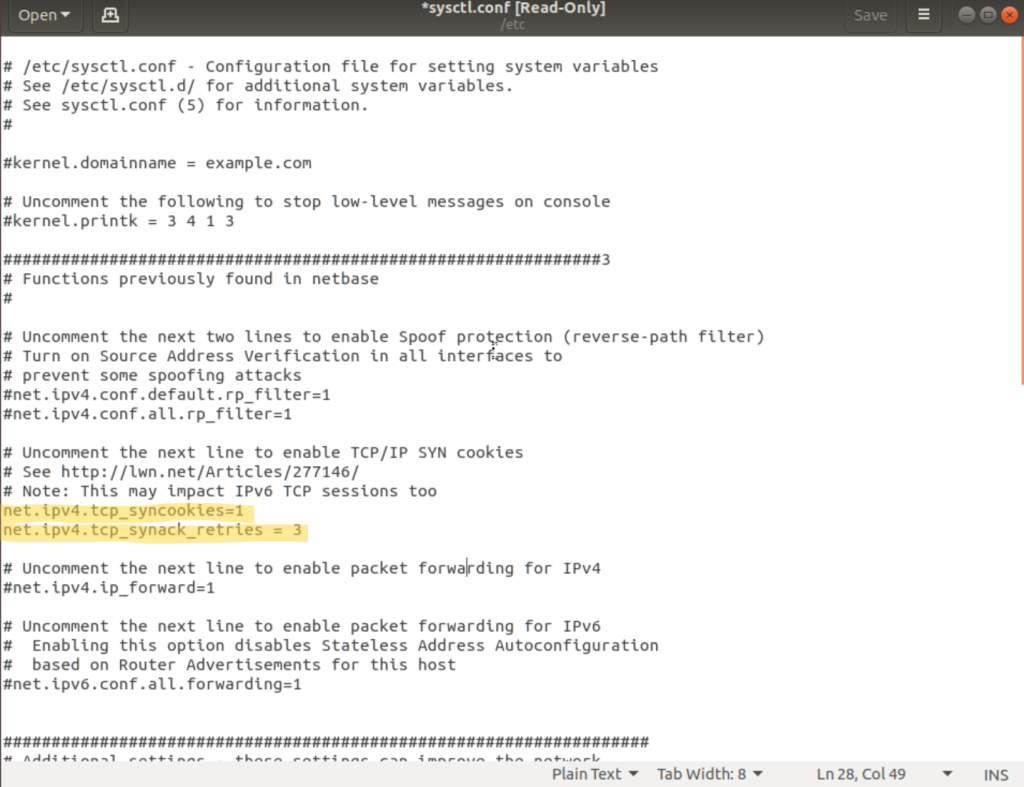
net.ipv4.tcp_syncookies = 1 — Enables SYN cookies, keeping server resources free until the full handshake completes.
net.ipv4.tcp_synack_retries = 3 — Reduces SYN/ACK retries from the default of 5, allowing faster packet processing.
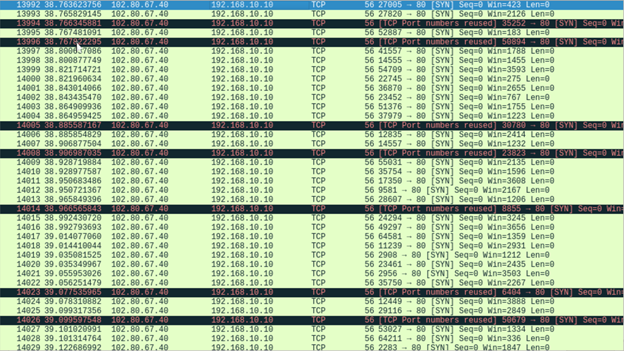
Video — website running during the SYN flood:
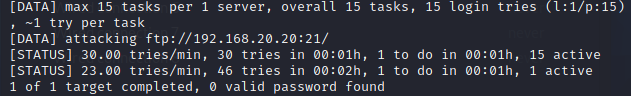
Hydra login cracker
Access Control Lists were configured on the defend router to restrict services to only trusted IP addresses, preventing future brute-force attacks.
ACL configuration
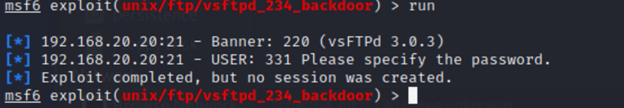
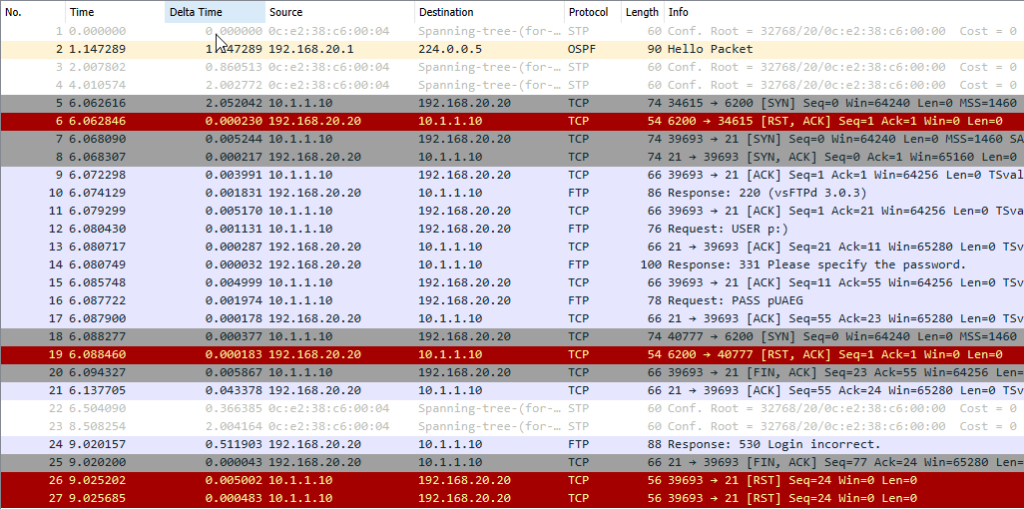
Metasploit reverse shell
The exploit was mitigated by updating the vulnerable VSFTPD service and restricting FTP access via ACLs.
Patching VSFTPD
VSFTPD version 2.3.4 contains the exploited backdoor. It was updated to version 3.0.3 using:
After updating, the exploit was run again. A connection was made but the exploit failed — the server was confirmed running version 3.0.3.